Exploited: The Cyber Truth

Exploited: The Cyber Truth
Podcast Description
Exploited: The Cyber Truth is a hard-hitting, no-fluff podcast exposing the realities of today’s cyber threat landscape and risks to critical infrastructure. Through candid conversations with top cybersecurity experts, industry leaders, and frontline defenders, the show breaks down recent high-profile vulnerabilities and exploits and covers innovative strategies used to stop them. To keep critical infrastructure safe, defenders need the upper hand. Tune in and get the cyber truth.
Podcast Insights
Content Themes
The podcast explores topics such as healthcare cybersecurity, automotive security, zero-day vulnerabilities, operational technology risks, and regulatory compliance, with episodes like 'Security Without Code Changes' addressing legislative impacts on medical device security and 'Shifting Cybersecurity Left in Automotive' discussing the Secure by Design approach for vehicle safety.

Exploited: The Cyber Truth is a hard-hitting, no-fluff podcast exposing the realities of today’s cyber threat landscape and risks to critical infrastructure. Through candid conversations with top cybersecurity experts, industry leaders, and frontline defenders, the show breaks down recent high-profile vulnerabilities and exploits and covers innovative strategies used to stop them. To keep critical infrastructure safe, defenders need the upper hand. Tune in and get the cyber truth.
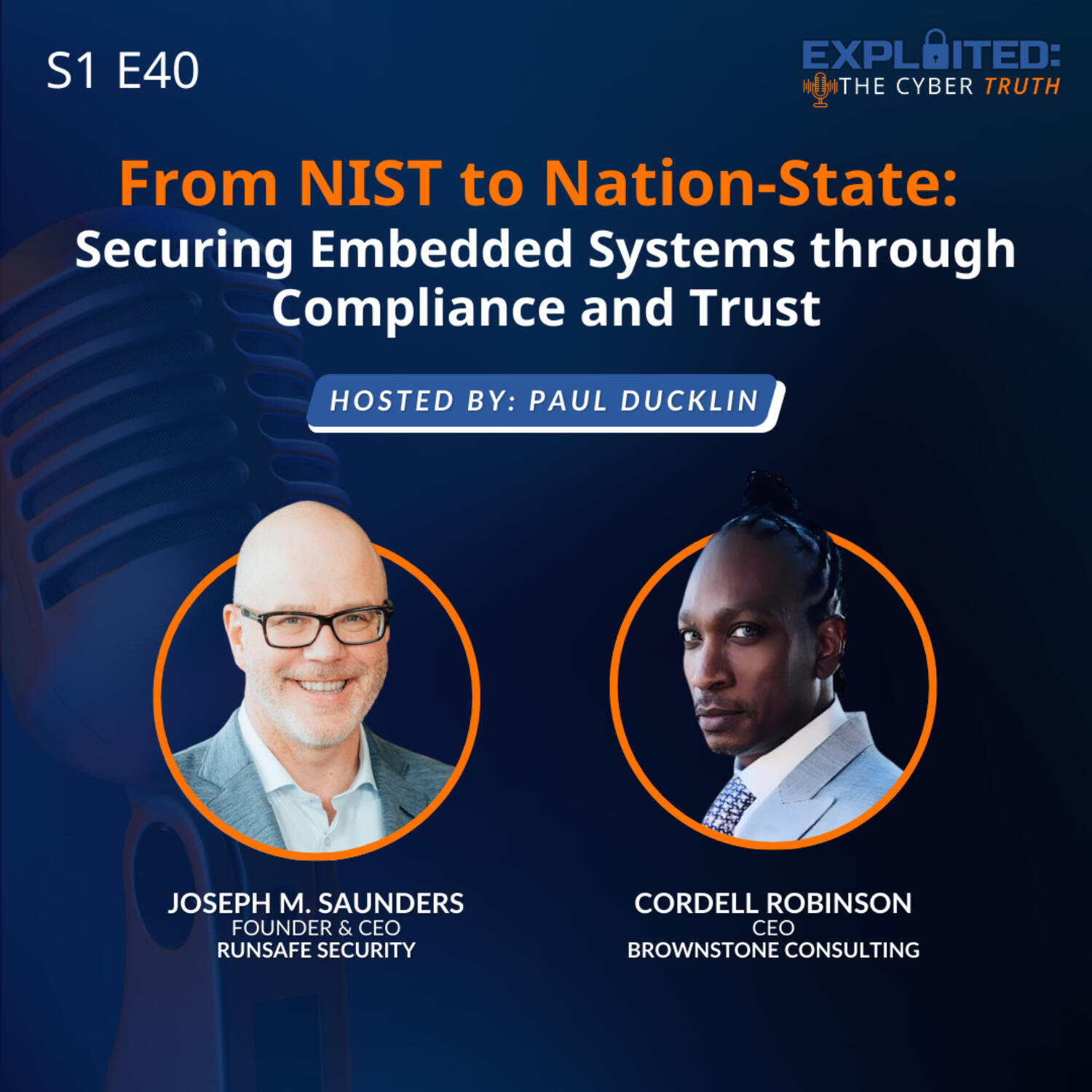
In this episode of Exploited: The Cyber Truth, host Paul Ducklin is joined by RunSafe Security CEO Joe Saunders and Cordell Robinson, CEO of Brownstone Consulting, to explore how security frameworks like NIST 800-53 are evolving from paperwork exercises into real drivers of security maturity.
From continuous monitoring and secure-by-design development to Software Bills of Materials (SBOMs) and vulnerability transparency, the conversation examines what it takes to build trust in embedded and operational technology (OT) systems, especially as regulators sharpen their focus and nation-state threats grow more sophisticated.
Together, they explore:
- Why compliance should cover people, processes, and technology—not just policies
- How NIST frameworks are shifting from checklists to operational rigor
- The growing importance of SBOMs in supply chain transparency
- How AI is reshaping both cyber defense and attacker capability
- What new regulatory pressure (including the EU Cyber Resilience Act) means for manufacturers
Whether you build embedded systems, ship software to government agencies, or manage critical infrastructure, this episode offers practical insight into building compliance programs that strengthen security and earn trust.
Disclaimer
This podcast’s information is provided for general reference and was obtained from publicly accessible sources. The Podcast Collaborative neither produces nor verifies the content, accuracy, or suitability of this podcast. Views and opinions belong solely to the podcast creators and guests.
For a complete disclaimer, please see our Full Disclaimer on the archive page. The Podcast Collaborative bears no responsibility for the podcast’s themes, language, or overall content. Listener discretion is advised. Read our Terms of Use and Privacy Policy for more details.