Entra.Chat

Entra.Chat
Podcast Description
Entra Chat is a weekly podcast hosted by Merill Fernando and delivers practical insights for Microsoft administrators and security professionals through conversations with identity experts who've been in the trenches.
Episodes feature seasoned Entra practitioners sharing real-world deployment experiences and Microsoft Entra team members who build the features you use daily.
Get the inside track on best practices, implementation strategies, and upcoming capabilities directly from those who design and deploy Microsoft identity solutions.
Join us for actionable takeaways you can apply immediately in your Microsoft 365, Azure, and Entra environments.
---
Entra.Chat, its content and opinions are my (Merill Fernando) own and do not reflect the views of my employer (Microsoft). All postings are provided “AS IS” with no warranties and is not supported by the author. All trademarks and copyrights belong to their owners and are used for identification only. entra.news
Podcast Insights
Content Themes
Focuses on Microsoft Entra, identity management, and security practices with episodes covering topics like 'From Okta to Entra: Migrating 700 Apps in 90 Days' and best practices for implementation strategies. The content emphasizes practical advice directly applicable in Microsoft 365, Azure, and Entra environments.

Entra Chat is a weekly podcast hosted by Merill Fernando and delivers practical insights for Microsoft administrators and security professionals through conversations with identity experts who’ve been in the trenches.
Episodes feature seasoned Entra practitioners sharing real-world deployment experiences and Microsoft Entra team members who build the features you use daily.
Get the inside track on best practices, implementation strategies, and upcoming capabilities directly from those who design and deploy Microsoft identity solutions.
Join us for actionable takeaways you can apply immediately in your Microsoft 365, Azure, and Entra environments.
—
Entra.Chat, its content and opinions are my (Merill Fernando) own and do not reflect the views of my employer (Microsoft). All postings are provided “AS IS” with no warranties and is not supported by the author. All trademarks and copyrights belong to their owners and are used for identification only.
If you can’t immediately name your break glass accounts and the last time you tested them → you’re already at risk.
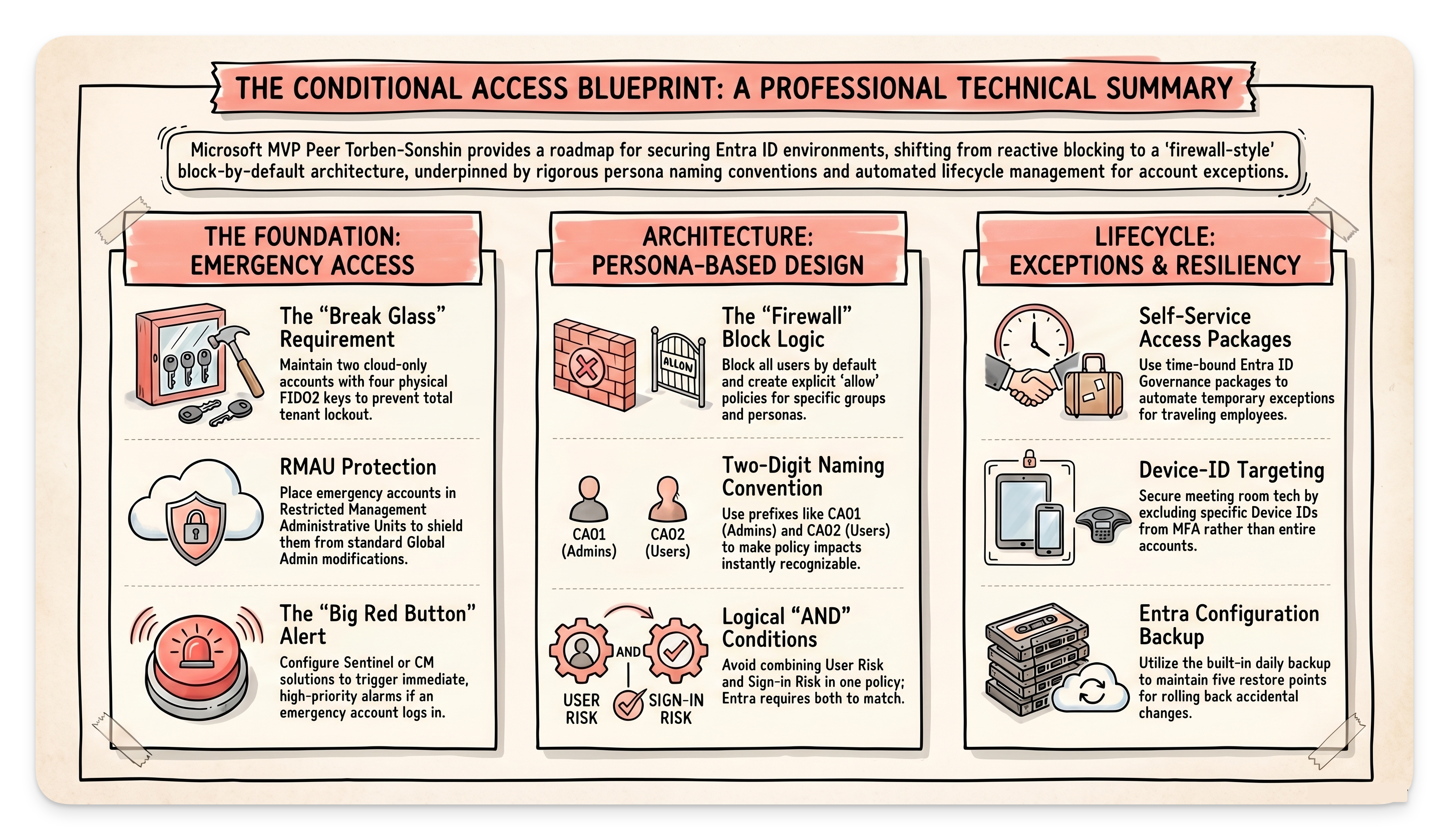
In this episode of Entra Chat, Microsoft MVP Per Torben walks through the conditional access mistakes he sees even large enterprises making, and the practical framework he actually uses with customers.
You’ll learn how to set up emergency access accounts the right way, why your CA policies should be built more like a firewall than a checklist, and the one naming convention that makes managing dozens of policies actually manageable.
🎧 Hit play, your tenant will thank you.
Sponsored by:
Entra ID Gaps That Cause Outages
In Microsoft Entra ID, outages often start small: an expired client secret, a lapsed certificate, or a suddenly failing integration. Traditional controls don’t track credential expiry or enforce application ownership, so issues appear only after something breaks.
Teams are left asking:
* Which applications can access Microsoft 365 data?
* Is that access still appropriate?
* Who owns the app?
Unclear answers stall reviews, weaken accountability, and slow delivery.
ENow App Governance Accelerator closes these gaps by highlighting expiring credentials, surfacing permission risks, and identifying ownership gaps before they disrupt operations. New Standard Tier pricing makes it accessible for organizations under 10,000 users, typically $3,500–$9,500 annually.
Subscribe with your favorite podcast player or watch on YouTube 👇
About Per Torben
Per Torben is a Senior Architect at Crayon and a Microsoft MVP for Identity and Access. Based in Norway, he frequently writes highly-read posts featured on Entra.News and runs the collaborative tech blog “Agder in the Cloud”.
LinkedIn – https://www.linkedin.com/in/pertorbensorensen/
🔗 Related Links
* Agder in the Cloud – https://agderinthe.cloud
* I.D.E.A. for creating/configuring break-glass accounts
* GitHub – https://github.com/Per-Torben/I.D.E.A.
* Blog – https://agderinthe.cloud/2026/01/06/introducing-i-d-e-a-and-i-d-e-a-001/
* Protected actions: https://agderinthe.cloud/2025/02/12/protected-actions-adding-extra-guards-to-your-entra-id-gate/
* Conditional Access hardeing (series): https://agderinthe.cloud/2024/12/05/how-to-fix-the-fundamental-flaw-in-conditional-access-part-1-introduction-and-coverage-gapsCA geo filter (series): https://agderinthe.cloud/2025/11/06/diving-into-geo-filter-with-entra-conditional-access-part-1
* Entra Backup – https://learn.microsoft.com/en-us/entra/identity/role-based-access-control/backup-restore
📗 Chapters
06:22 The importance of Break Glass accounts
09:02 Securing emergency access with FIDO2 and RMAUs
18:10 Configuring Conditional Access: The “Block by Default” strategy
27:26 Managing scope and preventing accidental lockouts
29:31 Persona-based naming conventions for CA policies
35:38 Grouping settings and avoiding bloated policies
41:54 Handling exceptions and travel access with Access Packages
44:55 The flaw in Protected Actions for Conditional Access
53:38 Using the new Entra Backup feature for quick restores
Podcast Apps
🎙️ Entra.Chat – https://entra.chat
🎧 Apple Podcast → https://entra.chat/apple
📺 YouTube → https://entra.chat/youtube
📺 Spotify → https://entra.chat/spotify
🎧 Overcast → https://entra.chat/overcast
🎧 Pocketcast → https://entra.chat/pocketcast
🎧 Others → https://entra.chat/rss
Merill’s socials
📺 YouTube → youtube.com/@merillx
👔 LinkedIn → linkedin.com/in/merill
🐤 Twitter → twitter.com/merill
🕺 TikTok → tiktok.com/@merillf
🦋 Bluesky → bsky.app/profile/merill.net
🐘 Mastodon → infosec.exchange/@merill
🧵 Threads → threads.net/@merillf
🤖 GitHub → github.com/merill
Get full access to Entra.News – Your weekly dose of Microsoft Entra at entra.news/subscribe
Disclaimer
This podcast’s information is provided for general reference and was obtained from publicly accessible sources. The Podcast Collaborative neither produces nor verifies the content, accuracy, or suitability of this podcast. Views and opinions belong solely to the podcast creators and guests.
For a complete disclaimer, please see our Full Disclaimer on the archive page. The Podcast Collaborative bears no responsibility for the podcast’s themes, language, or overall content. Listener discretion is advised. Read our Terms of Use and Privacy Policy for more details.